One-click security audits
for your entire fleet.
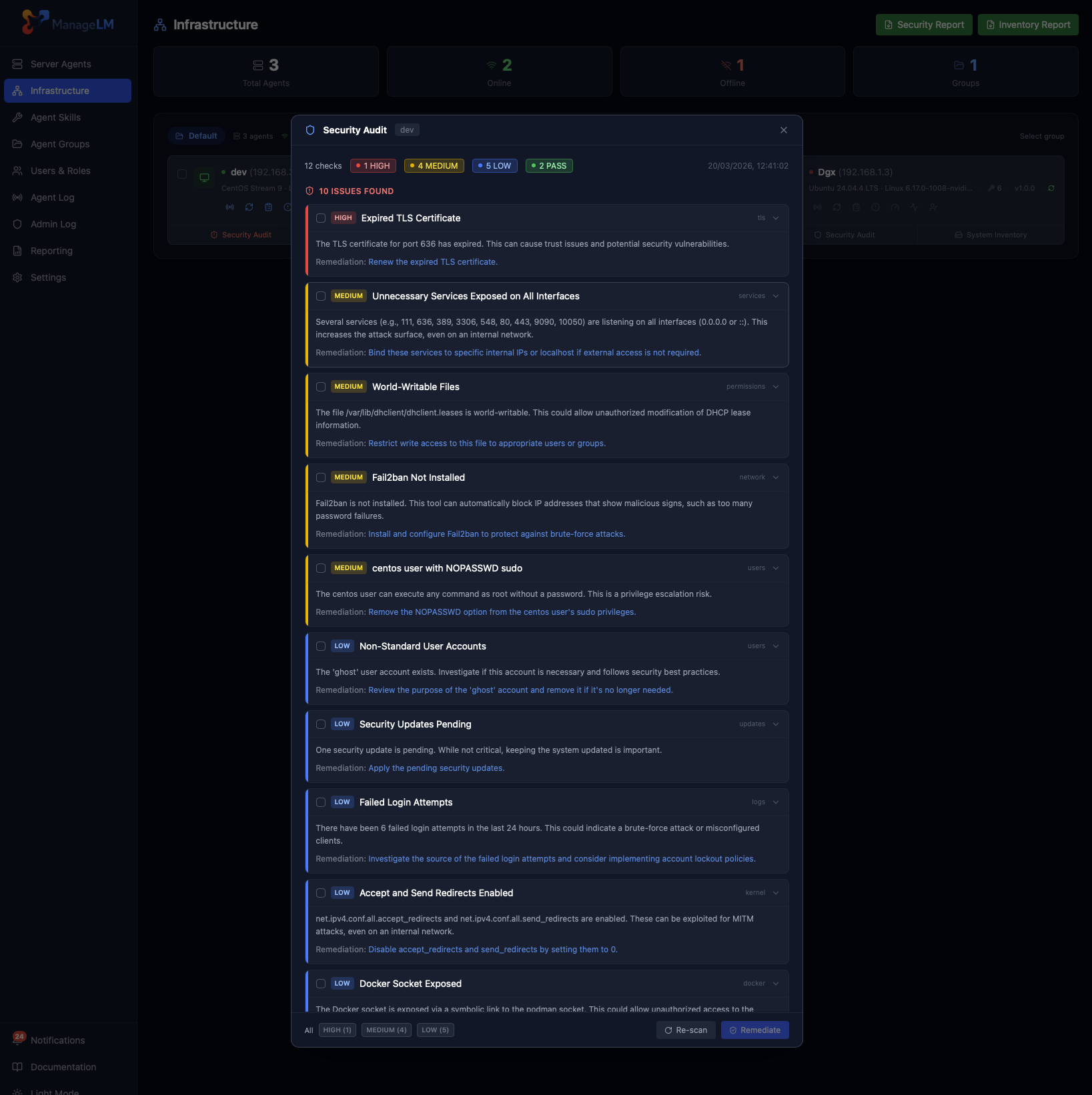
Deterministic, skill-free security scans across 18 hardening checks. Severity ratings adapt to each server's exposure, and remediation is one click away — on Linux, Windows, and everything in between.
On this page
Overview
The Security Audit is a deterministic, skill-free hardening scan that runs directly from the agent. No LLM calls, no external APIs — just read-only check commands executed inside a Landlock sandbox, with every finding evaluated against a strict rule set defined on the portal.
Unlike agentless scanners that ship a single profile for every server, ManageLM knows the context of each agent. A public, internet-facing box is held to a much stricter standard than an internal database server. Severity changes automatically, so your compliance score reflects actual risk — not theoretical checklist items.
Zero dependencies. No auditd, no osquery agent, no kernel modules. The checks reuse the same WebSocket channel the agent already uses for tasks, so there is nothing to install and nothing to punch through your firewall.
What gets checked
Each audit runs 18 checks across five categories. Findings are categorized, explained, and paired with a concrete remediation you can click to apply.
Authentication
SSH config, root login, password auth, MaxAuthTries, X11 forwarding, authorized keys across every user.
Network & Firewall
Listening TCP/UDP ports, UFW / firewalld / nftables / iptables rules, fail2ban status, kernel hardening sysctls.
TLS & Certificates
Weak protocols (SSLv3, TLSv1, TLSv1.1), legacy ciphers (RC4, DES, NULL), certificate expiry per listening port.
Privileged Accounts
UID-0 users, sudoers rules (including /etc/sudoers.d), SUID binaries, login users, NOPASSWD detection.
System State
Security updates pending, SELinux / AppArmor / Windows Defender, world-writable files, cron jobs.
Docker & Logins
Privileged containers, exposed Docker socket, root-running containers, failed SSH logins in the last 24 hours.
Vulnerability scanning
Installed packages matched against known CVEs. Actively-exploited vulnerabilities (CISA KEV) are automatically flagged Critical. Covers all major Linux distributions plus Python, npm, Go, Rust, Ruby, Java, .NET, and PHP packages — no configuration required.
How it works
Trigger
From the Infrastructure page, the Compliance dashboard, or via an MCP call from Claude. No configuration needed — the agent is ready as soon as it is online.Collect
The portal sends deterministic check commands (defined inreports/security.json) over the existing WebSocket. The agent executes them inside a Landlock read-only sandbox — it cannot modify disk during an audit.Evaluate
The portal runs the raw output through 23 compliance rules. Each rule produces a pass/fail with severity, framework tags (CIS, PCI-DSS, SOC 2), explanation, and remediation. A weighted score (0–100) is computed.Report
Findings appear in the audit modal and the Compliance dashboard. In-app notifications fire on completion, and drift alerts fire when a previously-passing rule starts failing.
Public vs. private context
ManageLM automatically classifies each agent as public (internet-reachable) or private (internal network) and adjusts severity accordingly. The same finding lands differently based on exposure:
| Finding | Public server | Private server |
|---|---|---|
| SSH root login enabled | Critical | Low |
| Missing firewall | Critical | Low |
| SELinux / AppArmor disabled | Medium | Low |
| Failed SSH logins > 100 / 24h | High | Medium |
| TLSv1.0 accepted | High | Low |
This context-aware scoring means your compliance dashboard shows real risk, not inflated noise. A lab VM with a relaxed configuration won't drag down the score of your production fleet.
One-click automated remediation
Select one or more findings, click Remediate, and the agent applies the recommended fixes intelligently — using its assigned Security & Hardening skill. Before every change, the agent:
- Backs up the original configuration file with a timestamped suffix.
- Applies the minimal change required by the remediation text.
- Validates the new config (e.g.
sshd -t) before restarting the affected service. - Rolls back automatically if validation fails.
Review before remediating. Always read the recommended fixes before clicking. Security changes like SSH hardening or firewall rules can lock you out if applied incorrectly — the agent validates, but you know your environment best.
PDF reports & scheduling
One Security button at the top of the Infrastructure page downloads a fleet-wide PDF report: summary bar with issue counts by severity, detailed findings with explanations and remediation, and a list of passed checks per server.
The Schedules popover turns any report into a recurring email — daily, weekly, or monthly — delivered to admin users who have report_ready notifications enabled. Changing the email schedule automatically syncs the scan schedule across all agents, so reports always reflect fresh data.
Compliance-ready. Every security finding is tagged with framework references (CIS, SOC 2, PCI DSS, ISO 27001, NIS2, NIST CSF, HIPAA). The same scan powers compliance reporting and auditor-ready evidence PDFs — no extra work.
Run your first audit in 60 seconds.
Install the agent, approve it in the portal, click Security. That's the whole workflow.