A complete PKI,
behind one button.
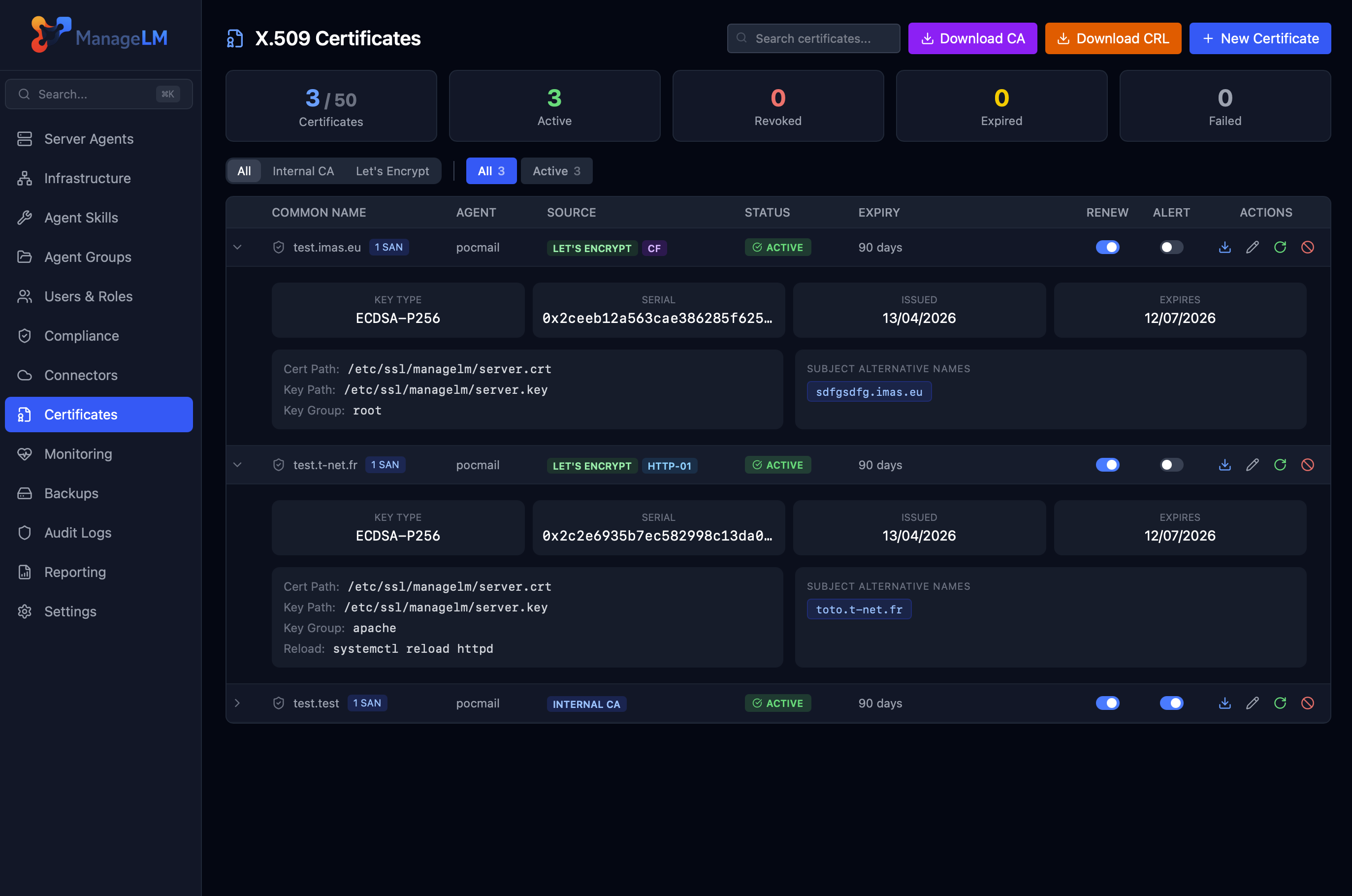
Run your own internal Certificate Authority or issue Let's Encrypt certificates — then deploy, renew, and revoke them directly to your agents. Private keys never leave the server they protect.
On this page
Overview
TLS certificates are a nightmare at scale. One expired cert brings down a service; one forgotten renewal triggers an outage at 3am. ManageLM bakes a full PKI into the portal: pick a source (internal CA or Let's Encrypt), set a validity window, click New Certificate, and the agent on the target server handles the rest — CSR generation, file deployment, service reload.
The design principle is simple: the private key never leaves the agent. The portal sees only the CSR and the signed certificate. Key compromise is impossible in transit because the key never transits.
Two certificate sources
Internal CA
Create or import an RSA-4096 root CA. Issue leaf certificates in ECDSA P-256, RSA-2048, or RSA-4096. Perfect for internal services, mutual TLS, and private deployments where public trust isn't needed.
Let's Encrypt ACME
Register an ACME account and issue free, publicly-trusted certificates. Both HTTP-01 and DNS-01 challenges are supported — including wildcard certificates via DNS-01.
HTTP-01 is the default: the agent handles the challenge on port 80 automatically — ideal for public-facing servers. DNS-01 goes further: the portal talks to your DNS provider (Cloudflare, DigitalOcean, Hetzner, OVH) and validates via DNS TXT records, which means any agent can get a certificate — public, private, or firewalled — and wildcards like *.example.com are supported out of the box.
Lifecycle
Issue
You pick an agent, a common name, and a file path. The agent generates a keypair and CSR locally. The portal validates, signs with the internal CA (or relays to Let's Encrypt via ACME), and streams only the signed cert back over WebSocket. The agent writes the cert + key to disk and reloads the target service.Renew
Manually with the Renew button, or automatically via the daily renewal sweep. Renewal mints a fresh keypair and CSR on the agent, signs a new cert, deploys it, then revokes the old one. LE renewals also notify Let's Encrypt to revoke the outgoing cert server-side.Revoke
Mark a certificate as revoked and the portal updates the CRL immediately. LE revocations propagate to Let's Encrypt's ACME endpoint. Internal CA revocations can be reactivated; LE revocations are final.Delete
Soft-deletes the certificate metadata. The serial stays in the CRL until the natural expiry date, at which point the daily sweep purges it.
Security model
Private keys stay on the agent. The agent generates the keypair during CSR creation; only the CSR is transmitted. The portal never sees — and therefore cannot leak — the private key material. Even a full portal database compromise would not expose any TLS private key.
- Transport — all portal ↔ agent traffic rides the existing mTLS-authenticated WebSocket connection. No separate channel, no side-deployed tooling.
- Signing material — internal CA private keys are stored AES-256-GCM encrypted at rest with account-scoped keys.
- Auditability — every issue / renew / revoke produces a portal audit log entry with user, agent, timestamp, and source IP.
- Role-based control — CA and LE account management is restricted to the account owner; the
perm_certificatespermission controls day-to-day operations.
Automatic renewal
A daily background task handles the entire certificate lifecycle without human involvement. It is Redis-locked for high availability (safe for the DNS round-robin portal pair) and runs through four stages:
- Expire certificates whose
not_afterhas passed. - Renew active certificates inside the renewal window (7–90 days before expiry, configurable), but only on online agents.
- Purge soft-deleted certificates whose serial has naturally expired.
- Notify admins via in-app, email, and webhook on renewal success or failure.
Configure the default validity (14–365 days), key type, and renewal window once in Settings → PKI & CA. New certificates inherit the defaults — no per-cert boilerplate.
CRL & public endpoints
The portal exposes two unauthenticated endpoints used by TLS clients and auditors:
| Endpoint | Purpose |
|---|---|
/pki/<crl_id>.crl | DER-encoded Certificate Revocation List, signed by the internal CA, cached in Redis with 7-day validity |
/pki/<crl_id>.cer | DER-encoded CA certificate for trust chain installation |
Both URLs are embedded in every issued certificate as CRL Distribution Point and Authority Information Access extensions — so TLS clients can fetch trust and revocation data without extra configuration.
Pairs with Service Monitors. Flip a monitor into TLS mode and it will warn you before any certificate expires — whether issued by ManageLM, Let's Encrypt, or something else entirely. Two systems, one safety net.
Stop dreading renewals.
Set up a CA or connect Let's Encrypt in minutes. ManageLM handles every renewal from here.