Know who has access to what.
Map every SSH key and sudo privilege across your infrastructure. Fingerprints get matched to your team in the portal, so you see who can reach which server — and exactly what they can do once they're in.
On this page
Overview
Access sprawls fast. SSH keys get copied, service accounts accumulate, /etc/sudoers.d fills up with one-off rules. Nobody can remember who has what access to which machine — and that's exactly what auditors and attackers love to find.
The SSH & Sudo access scanner reads the authoritative sources on each agent (~/.ssh/authorized_keys, /etc/sudoers, group membership) and builds a fleet-wide access map. Every discovered SSH key is fingerprinted and matched against the public keys registered by your ManageLM team members, giving you real identity — not comment-line guesses.
No LLM needed. The scanner is fully deterministic. Check commands defined on the portal, executed inside a Landlock read-only sandbox on the agent, results returned and rendered. Zero AI calls, zero side effects.
What is collected
| Data | Source | Details |
|---|---|---|
| SSH authorized keys | ~/.ssh/authorized_keys | Key type, SHA-256 fingerprint, comment, full public key, source file, line number |
| Sudo user rules | /etc/sudoers + drop-ins | Target host, runas user, allowed commands, NOPASSWD flag |
| Sudo group rules | Sudoers + /etc/group | Group rules like %wheel expanded to individual users |
Every drop-in file under /etc/sudoers.d/ is parsed too. Group-based rules (e.g. %wheel ALL=(ALL) ALL) are expanded against actual /etc/group membership, so you see the real human that a rule grants access to — not just a group name.
Identity mapping
Each ManageLM user can register one or more SSH public keys in their profile (Settings → Security → SSH Public Keys). When the scanner discovers a key on a server, its SHA-256 fingerprint is matched against every registered profile key. Matched keys display the user's name in a green badge; unmatched keys show as Unknown.
Fingerprint-based
Identity is resolved exclusively by SHA-256 fingerprint. The user@host comment in authorized_keys is never trusted — it's informational at best, spoofable at worst.
Unknown key surfacing
Any key without a matching profile is explicitly labeled "Unknown" — the fastest way to spot orphaned access or rogue deployment keys.
NOPASSWD alerts
Sudo rules with NOPASSWD are highlighted in red as a security concern — a common foothold for lateral movement after SSH compromise.
Group expansion
Rules like %wheel are expanded to actual group members — so "who is in wheel?" is visible without cross-referencing /etc/group manually.
Register your team's keys. Identity resolution only works when team members have added their SSH public keys in the portal. Without them, every discovered key appears as "Unknown" and the mapping collapses to a pile of fingerprints.
Natural-language access control
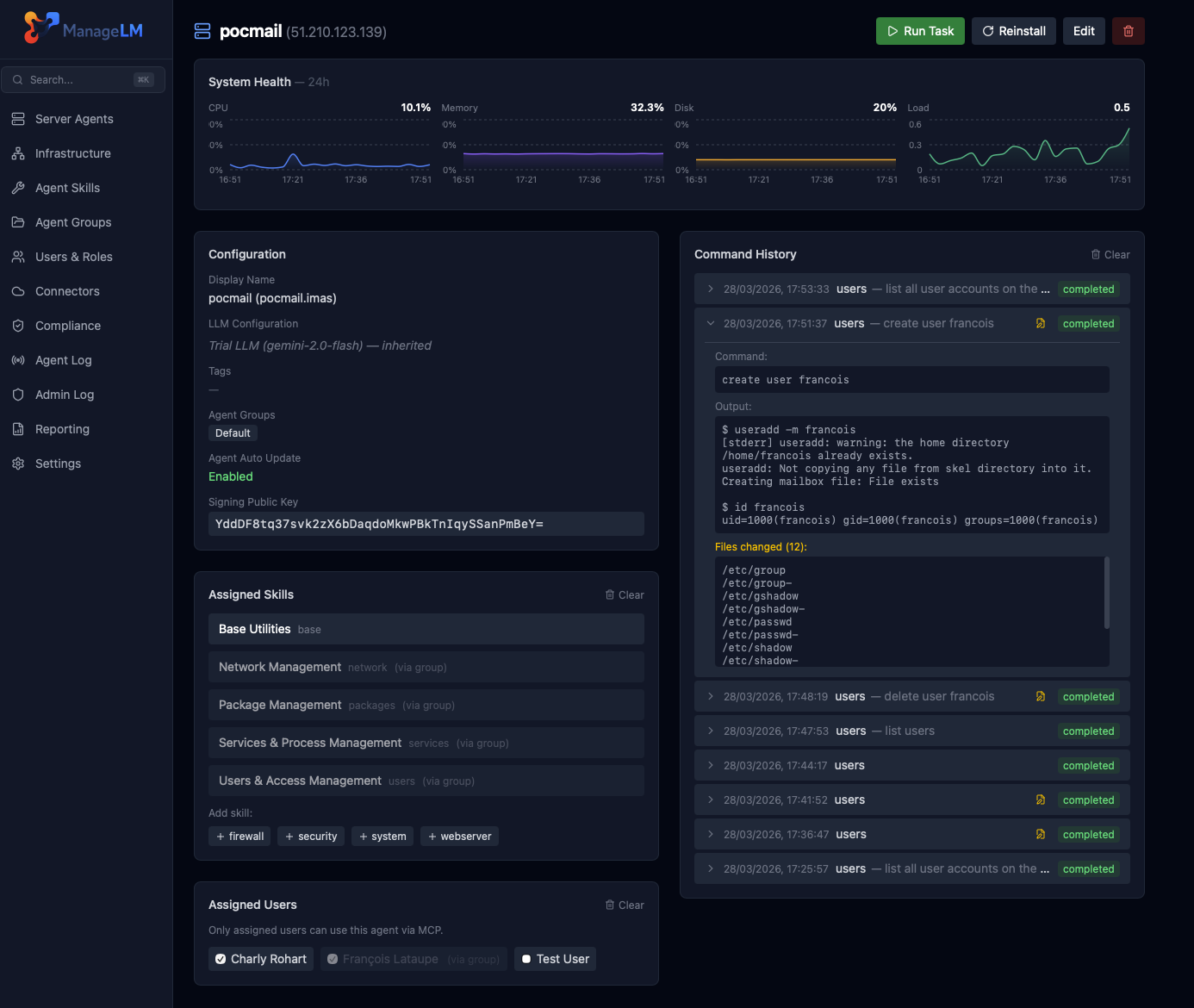
Once ManageLM knows who has what, you can manage access in plain English through Claude, ChatGPT, Slack, or the portal's shell. The access data powers five MCP tools that work together with the users skill:
| Ask | What happens |
|---|---|
| "Who has SSH access to pocmail?" | Lists every registered & unknown key found on pocmail |
| "Show me Charly's sudo authorizations" | Fleet-wide sudo rules granted to Charly, with NOPASSWD flagged |
| "List all NOPASSWD sudo rules on production" | Returns every passwordless sudo rule on production-tagged agents |
| "Give Charly SSH access to pocmail" | Looks up Charly's registered key, deploys it via the users skill |
| "Remove all access for Yoann" | Fleet-wide SSH key + sudo rule removal for the named user |
Reports & scheduling
The SSH & Sudo button at the top of the Infrastructure page downloads a fleet-wide PDF access report: one section per user, one section per server, NOPASSWD rules flagged in red, orphaned keys listed separately.
Schedule recurring scans per-agent or fleet-wide from the Schedules popover — daily, weekly, or monthly. The scheduler runs every 15 minutes and prioritizes agents that have never been scanned.
Drift you can actually see. Because scans are deterministic and scheduled, new keys or new sudo rules show up on the next run. Pair that with the security audit's drift notifications to catch unauthorized changes early.
Audit your access in one click.
Run a scan now. Fifteen seconds later, you'll know who holds which keys across your entire fleet.