See what an attacker sees.
Automatically.
Automated penetration testing that scans your public servers from the outside. nmap, nuclei, testssl.sh and more — orchestrated end-to-end, AI-summarized, and mapped to compliance frameworks.
On this page
Overview
Built-in security audits tell you what is wrong inside your servers. Pentests answer the complementary question: what can an attacker reach from the outside? ManageLM runs industry-standard offensive tools against your public endpoints in a controlled, repeatable way — no VM to maintain, no Kali instance to stand up, no one-off scripts.
Behind the scenes, a dedicated pentest service orchestrates nmap, nuclei, testssl.sh, ffuf, subfinder, and a suite of purpose-built checks. Results are returned to the portal, summarized by an LLM into plain-English findings, and mapped to compliance controls automatically.
Available on Pro & Business plans. Pentests consume credits — Pro and Business plans include a bundle, and you can top up from Settings → Account. Only successful scans are charged; failures and cancellations are free.
Available tests
Nine test types cover the full external attack surface. Run them individually or bundle several into a single scan — credits are consumed per test, and URL-based tests run once per target URL.
| Test | What it does | Credits |
|---|---|---|
| Basic Scan | Port discovery (nmap) + vulnerabilities (nuclei) + TLS quick check | 3 |
| Full Port Scan | All 65,535 TCP ports — finds the forgotten services | 3 |
| Vulnerability Scan | Extended nuclei templates covering critical / high / medium CVEs | 3 |
| SSL/TLS Audit | Full testssl.sh analysis — protocols, ciphers, chain, HSTS, vulnerabilities | 1 / URL |
| Web App Scan | Nuclei web templates — exposed panels, default creds, misconfigs | 3 / URL |
| DNS Audit | SPF, DMARC, DKIM, MX records — email spoofing & DNS hygiene | 1 / URL |
| HTTP Headers | Security headers analysis — CSP, HSTS, X-Frame-Options, etc. | 1 / URL |
| Directory Scan | Common path discovery with ffuf — backup files, config leaks | 2 / URL |
| Subdomain Enum | Passive subdomain discovery with subfinder | 1 / URL |
How it works
Select targets
Open the Pentests page, pick one or more public agents, select the tests to run, and add target URLs if needed. The portal estimates credit cost upfront.Prove ownership
The portal mints a one-time validation token. The agent contacts the pentest service from its public IP and proves it controls the target — preventing you (or anyone else) from scanning hosts they don't own.Scan
The pentest service runs the selected tools sequentially against your endpoints. Raw output is captured and timestamped.Summarize
An LLM reads the raw tool output and generates a human-readable report with severity-rated findings, remediation guidance, and a 0–100 security score. Raw output is preserved as evidence.
Ownership & safety
Pentesting is a sharp tool — ManageLM is built so it can only cut your own grass. Multiple layers prevent misuse:
- Public agents only — the target must already be an installed ManageLM agent that you control.
- Agent-side validation — a one-time token exchanged over the agent's public IP confirms control. No proxying, no tunneling tricks.
- Domain verification — URL-based tests require a DNS TXT record proving you own the domain. Verification is cached for 24 hours before re-proof is required.
- DNS resolution check — target URLs must resolve to the agent's public IP, so you cannot scan a third-party host that happens to be in the same IP range.
- One scan per agent — rate limiting prevents both accidental runaway scans and parallel abuse.
AI-generated reports
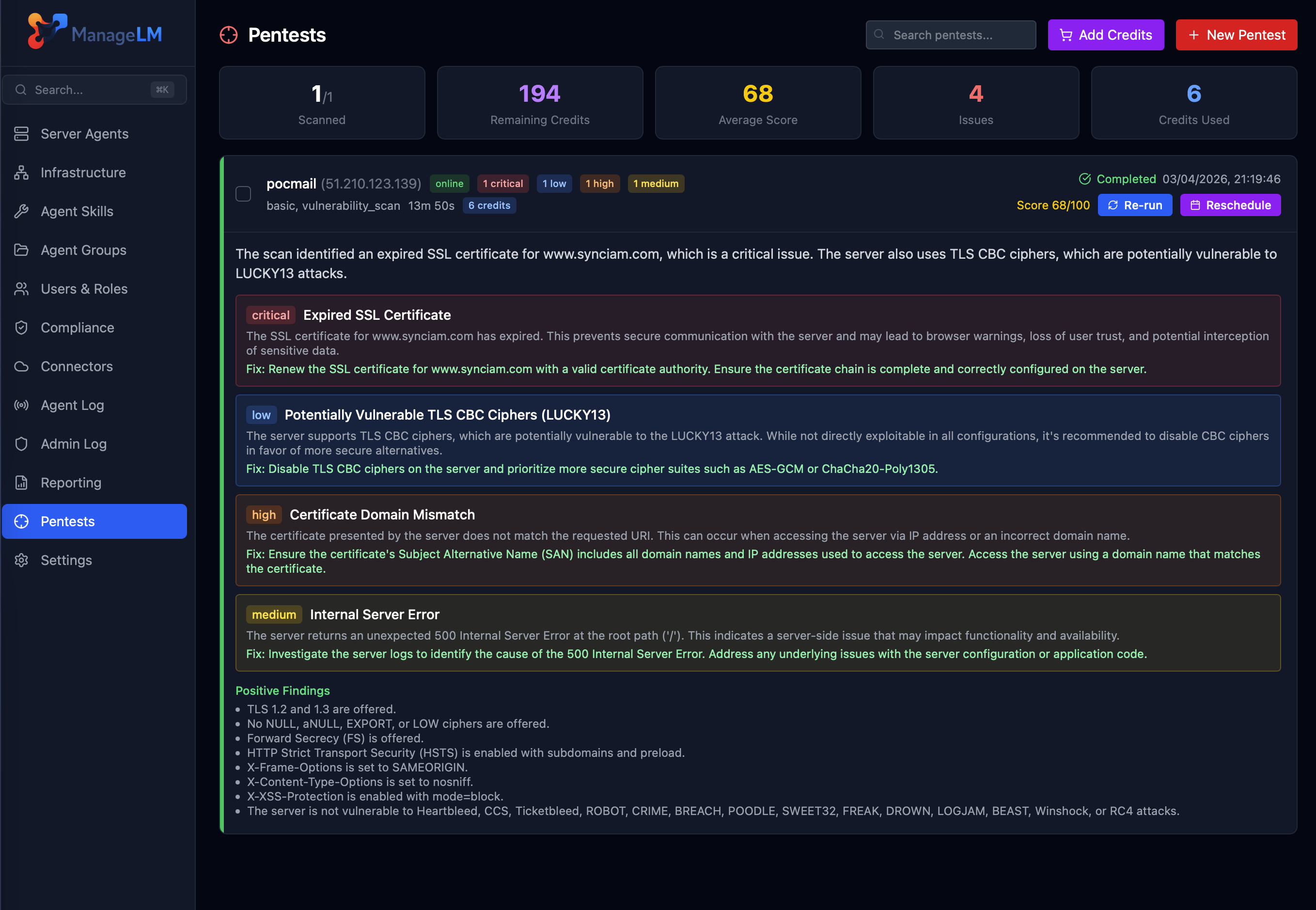
Raw nmap and nuclei output is powerful but noisy. ManageLM feeds every scan result into an LLM that extracts real findings, classifies severity, and writes the remediation section in the voice of a senior security engineer. What you see is:
Security score
0–100 weighted by finding severity, so you can track trend over time — per agent and fleet-wide.
Grouped findings
Open ports, exposed services, missing headers, weak TLS, web misconfigs — each with a one-line summary and full context.
Per-finding remediation
Concrete steps to fix each issue, tailored to the service detected (nginx vs. Apache, systemd vs. Windows Services).
Raw tool output
Every finding links back to the raw tool output — useful for auditors, root-cause analysis, and export pipelines.
Compliance integration
Pentest results don't live in a silo. Each tool produces pass/fail rules that map directly to compliance framework controls:
- CIS Level 1 — weak TLS, exposed services, missing firewalls.
- PCI DSS v4.0 — cardholder data environment segmentation, external vulnerability scans.
- ISO 27001:2022 Annex A — vulnerability management and secure configuration controls.
- NIS2, NIST CSF, SOC 2, HIPAA — all mapped automatically.
Run a pentest, and the same data feeds your framework coverage, drift detection, and evidence PDFs. A single scan can satisfy multiple audit requirements.
Pairs perfectly with Security Audit. Internal audits find configuration weakness; pentests find exploitable exposure. Together they give you the full picture — the defender's checklist and the attacker's playbook.
Scan from the outside.
Start with a Basic Scan on any one of your agents. 3 credits, roughly two minutes, zero setup.